So I'm forced to learn and install Windows Server 2012 R2, quickly. Thanks to some hacker's ransomware for my school. It happened once before, but files were encrypted through a regular user's account. The server's system weren't affected. But this time, they are.
This happened right after I restricted inbound RDP to certain IPs in the firewall. So the hack must have gotten in from one of the networked machines, which I did not block. With Win Server 2018, it seems that there was no way to monitor this type of attack.
Hopefully, Windows Server 2012 R2 can do a better job. Had to put this on a 64-bit machine. A few changes for the users: be serious about hard to guess passwords.
Something that always bugs me is this CAL licensing. I think now I understood a bit: A CAL (license) is what allows ONE user to logon to the server (locally). Remotely, you need an RDS CAL (on top of the one CAL), because RDS CAL is only for the user's remote session while the CAL is what allows the server to allow the user to logon on it. Of course, RDS CAL is also differentiated between RDS user CAL and RDS device CAL. What was described above is for RDS user CAL. For the Device CAL, it just means instead of the user being licensed, it's the user's device that's been licensed (so I guess it doesn't matter who logs in as long as it's the licensed device).
Somehow it took me a while to find out information about purchasing such licenses. I think Windows Server has its own license (around $100 for now). But for a Windows Server 2012 R2 10 User CAL, it's around $130 now, while 10 RDS User CAL costs about $370. They are apparently valid for a lifetime.
That means, from square one, a Windows Server 2012 R2 with 10 RDS user licenses costs about: $100 + $130 + $370 = $600. 10 is enough for my school for now, but 20 would be preferred, which would cost $1,100 total.
Nevertheless, there are some sites that claim that we can reset the grace period of 120 days of Unlimited RDS CAL. One is to delete a value in the registry:
Delete the REG_BINARY (i.e. L$RTMTIMEBOM****) in: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\RCM\GracePeriod
To delete the key you must take ownership and give admin users full control.
After a restart of the server RDS will reset the grace period to 120 days. This has worked for me.
slmgr /rearm
in powershell as administrator. In case the previous method fails.
To find out how many grace period is left, run powershell as administrator and use this command:
(Invoke-WmiMethod -PATH (gwmi -namespace root\cimv2\terminalservices -class win32_terminalservicesetting).__PATH -name GetGracePeriodDays).daysleft
As for Windows Server 2012 R2 itself, there's also a way to keep reactivating it:
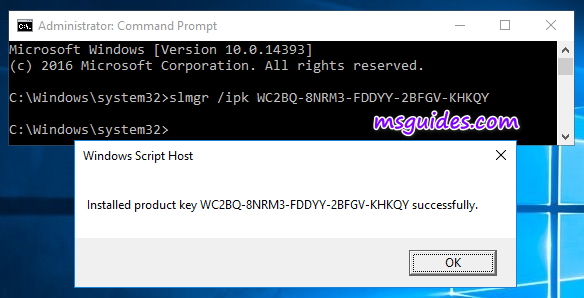
- Get the right product key from the official article of Microsoft.The KMS Client Setup Key of WS 2016 Standard is “WC2BQ-8NRM3-FDDYY-2BFGV-KHKQY”. I will use it in the next step.

- Install the key on your server.To open command prompt, click on the Windows button, search for “cmd” and run the command prompt as administrator. Then, enter “slmgr /ipk CLIENTKEY” in the command window.
Note: each command is followed by hitting Enter.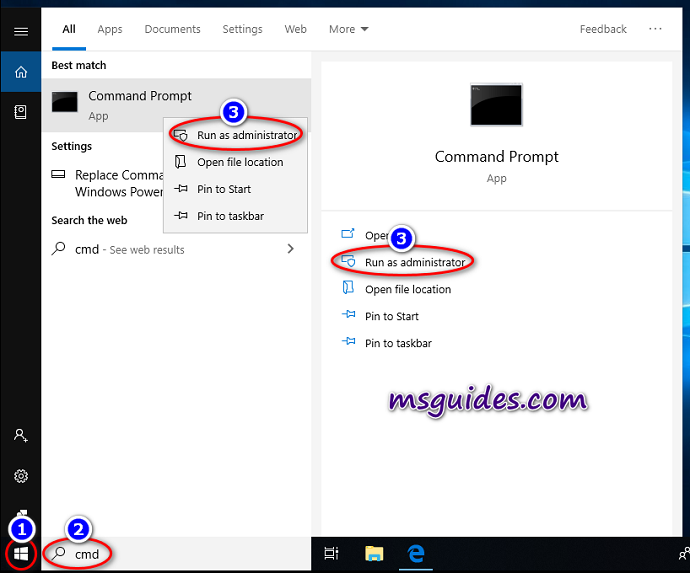
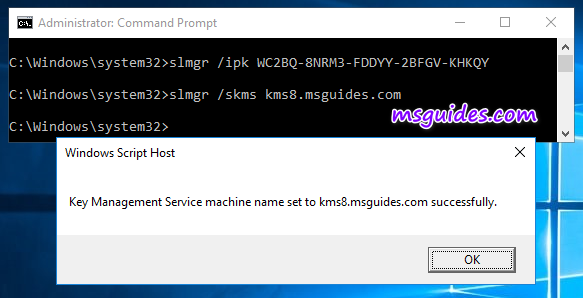
- Set the KMS server.Enter “slmgr /skms kms8.msguides.com” in the window.
- Activate the KMS client key.Finally, use the command “/ato” to activate your Windows.
I tried the KMS product key (D2N9P-3P6X9-2R39C-7RTCD-MDVJX) for my 2012 R2 Standard edition and it seems to work (for now).

thanks , i am a little afraid of using the KMS product key, can i get a retail key from keyingo.com, it does not cost too much
Never heard of it, I wouldn't trust it personally
As a side note, when encountering Windows 7 Ultimate's message: windows 7 build 7600 "this copy of windows is not genuine", the quickest fix would be to reset the 30 day free trial period by going to cmd in administrator mode, and type in "SLMGR -REARM". Works great! But of course, after 30 days, the problem may come back again. I'll look into it when the time comes, as there seems to be tons of talk about getting around it on FB, etc.